Your vendor questionnaire is a time capsule. It tells you what a supplier's security posture looked like on the day someone filled it out — which is to say, it tells you almost nothing about what's happening in your CI/CD pipeline right now.
March 2026 made that argument for us, in the most concrete terms possible.
Two Attacks, One Uncomfortable Lesson
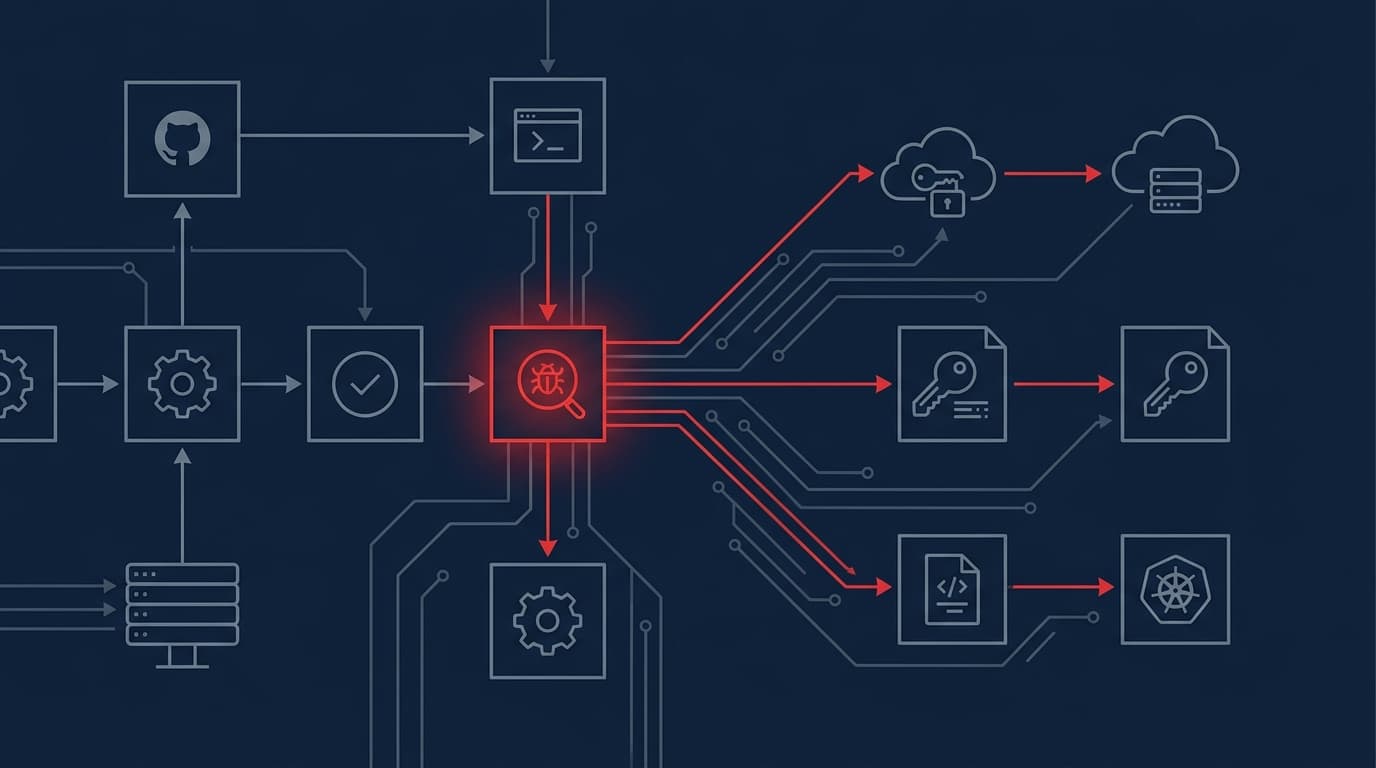
Between late February and March, two separate threat groups compromised tools that sit at the heart of modern software development. TeamPCP — a loosely organized crew with operations dating back to at least September 2025 — hit Trivy, an open-source vulnerability scanner with over 100,000 users embedded in thousands of CI/CD pipelines. They injected credential-stealing malware through GitHub Actions and container images, hoovering up CI/CD secrets, cloud credentials, SSH keys, and Kubernetes configuration files. Then they used what they stole from Trivy to pivot into additional open-source tools, including KICS and LiteLLM.
Separately, North Korean-linked actors went after Axios — a JavaScript library running in roughly 80% of cloud and code environments, with around 100 million weekly downloads. The Register reported that both campaigns are expected to play out over months, with Mandiant Consulting CTO Charles Carmakal noting that exfiltrated data "will likely be leveraged this week, next week, next month — probably for several months."
Unit 42's analysis puts the current scope of the TeamPCP operation at data exfiltrated from 500,000 infected machines, with over 300 GB of secrets exposed across organizations in every business vertical. Those numbers are sourced from vx-underground and should be treated as estimates — but even half that figure is a catastrophe.
Here's what makes these attacks particularly instructive: Trivy is a security tool. It runs with elevated privileges by design. TeamPCP didn't just find a path through the supply chain — they weaponized the infrastructure organizations trust to protect them. That's not a gap an SBOM closes.
What Compliance Theater Actually Costs You
The standard enterprise response to supply chain risk is a vendor questionnaire, a SOC 2 report request, and a checkbox in a GRC platform. Safe Security's analysis puts the failure rate of this approach in stark terms: 45% of organizations have experienced third-party related business interruptions in the past two years, representing 68% year-over-year growth in third-party incidents.
That growth is happening while SBOM mandates are expanding and vendor risk programs are proliferating. The compliance activity is increasing. The incidents are also increasing. Those two facts belong in the same sentence.
The core problem is that an SBOM tells you what components are in a piece of software at a point in time. A vendor questionnaire tells you what a vendor's security team was willing to write down. Neither tells you what happens to your operations when that vendor gets compromised — and neither would have flagged Trivy as a risk before March 16, because Trivy wasn't compromised before March 16.
What actually matters is dependency mapping that's continuous, not periodic — understanding which vendors have privileged access to your build environment, which open-source packages are embedded in your CI/CD pipelines, and what your blast radius looks like when (not if) one of them gets hit. That's a fundamentally different operating model than compliance checkbox security, and most enterprise programs aren't built for it.
What to Do Before the Next Trivy
The Cisco Talos assessment quoted in The Register's coverage is worth sitting with: attackers are increasingly using AI to make social engineering campaigns "more believable and hyper-personalized." The Axios compromise involved North Korean operators who understood developer environments well enough to execute a targeted campaign against a library with nine-figure weekly download counts. That's not a phishing email from a Nigerian prince. That's a sophisticated operation targeting the exact tools your developers trust implicitly.
Concrete steps that actually move the needle:
Audit what's running in your CI/CD pipelines with elevated privileges. Security scanners, AI gateways, package managers — anything that touches secrets or has write access to your build environment is a high-value target. Treat it accordingly.
Pin your dependencies and verify checksums. The TeamPCP attack propagated through GitHub Actions and PyPI. Unpinned dependencies in automated workflows are an open door.
Map your blast radius before an incident, not during one. If a critical open-source tool in your pipeline were compromised tomorrow, how long would it take you to identify every system that touched it? If the answer is "days," that's your actual risk posture — not your vendor's SOC 2 score.
The Trivy and Axios campaigns will continue generating follow-on incidents through at least mid-2026. Watch for threat intelligence updates from Mandiant and Unit 42 as the full scope of credential exposure becomes clearer — the 500,000-machine estimate is almost certainly a floor, not a ceiling.